By Mary Clare Jalonick and Jake Pearson / Associated Press
WASHINGTON — A U.S. senator wants to know how well the country’s top six voting machine manufacturers protect themselves against cyberattacks, a move that comes just weeks after federal authorities notified 21 states that they had been targeted by Russian government hackers during the 2016 presidential election
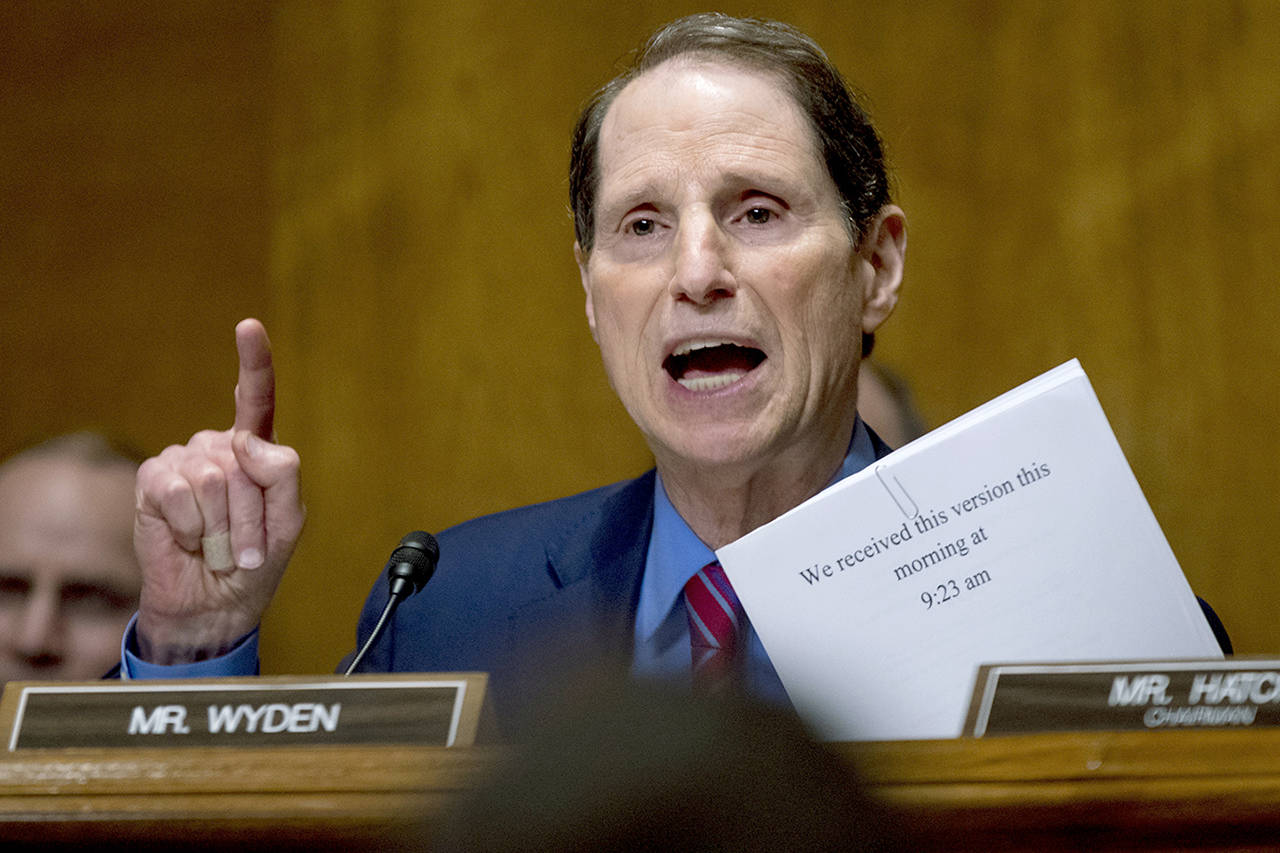
In a letter Tuesday to the CEOs of top election technology firms, Sen. Ron Wyden writes that public faith in American election infrastructure is “more important than ever before.”
“Ensuring that Americans can trust that election systems and infrastructure are secure is necessary to protecting confidence in our electoral process and democratic government,” writes Wyden, an Oregon Democrat.
An assessment by the Department of Homeland Security found that Russian hackers targeted state election systems. Some states have since disputed that claim.
A representative for Election System & Software said the company had not yet received Wyden’s letter. Steven Sockwell, a spokesman for Austin, Texas-based Hart InterCivic, which has provided vote tabulation devices, software and other voting services in 18 states, said he wasn’t aware of any cyberattacks on the company or its products.
Company representatives at Dominion Voting Systems, Unisyn Voting Solutions, MicroVote and Five Cedars Group did not respond to requests for comment.
DHS officials said in June congressional testimony that Russian hackers didn’t target U.S. elections infrastructure “involved in vote tallying,” but said a state board of elections website had been compromised, among other cyber activity. Officials have yet to release a detailed account of attempted and successful breaches in those states.
A top-secret National Security Agency report leaked to the online news site The Intercept this summer detailed a Russian military-orchestrated hacking campaign in August 2016 that targeted a Florida-based software vendor with fake, phishing emails. That vendor manages voter registration and voter rolls in eight states, though the document said it was “unknown” to what extent the cyberattack compromised local election systems.
A top federal cyber official has likened most of the Russian cyber attempts on state election systems in 2016 to “somebody walking down the street and looking to see if you are home.”
“A small number of systems were unsuccessfully exploited as though somebody had rattled the doorknob but was unable to get in, so to speak,” said Samuel Liles, who runs the cyber division of DHS’s intelligence and analysis office. But, he said, in a small number of cases “they made it through the door.”
In his letter, Wyden asks the companies to detail their internal security protocols, including whether they test their systems against penetration attempts by outside experts and if they follow federal best practices.
In the wake of Russian interference in the 2016 presidential campaign, federal officials designated elections systems critical infrastructure on the order of power plants or electrical grids. But state elections officials have expressed confusion over what that designation entails, and some states chafe at the prospect of losing local control of their elections systems.
Pearson reported from New York.
Talk to us
> Give us your news tips.
> Send us a letter to the editor.
> More Herald contact information.